It is simpler than you would think to gain access to the dark web. In fact, you have most likely already done so. The media has done a poor job of distinguishing between the deep web and the dark web–two similar titles for two very distinct entities.
Definition of the dark web
The dark web is a secret network of internet sites that can only be accessed with a specialised web browser. It is used to keep online activity secret and anonymous, which may be useful in both legal and illicit uses. While some people use it to avoid government restrictions, it has also been used for very unlawful conduct.
What is the difference between the dark web, the deep web, and the surface web?
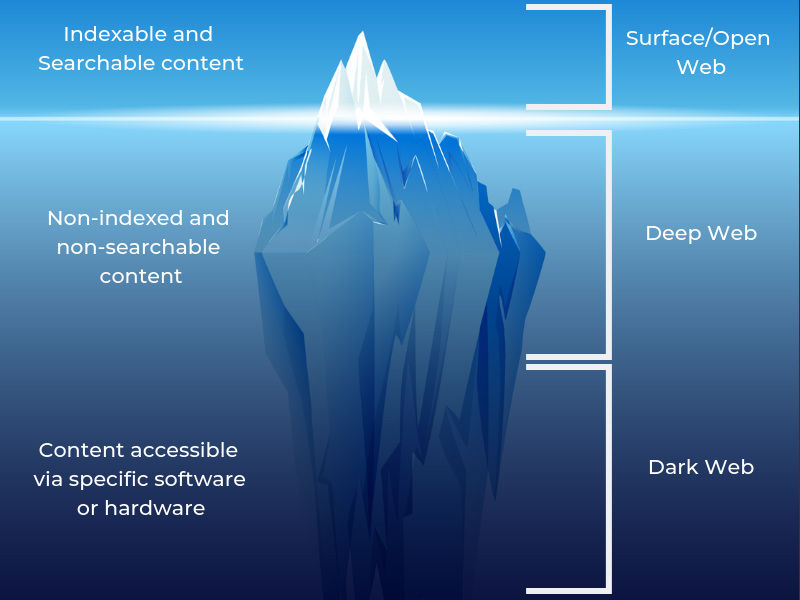
The Internet is vast, with millions of web pages, databases, and servers operating around the clock. However, the “visible” Internet sites that can be accessed using open free and basic search engines such as Google and Yahoo — is only the tip of the iceberg.
There are various terminology associated with the non-visible Web, but it’s important to understand how they vary if you want to go off the main road.
The dark web is a small section of the deep web. Dark web domains are frequently connected with criminal behaviour–but not always. More on it in a moment. It is reasonably safe to access material on the deep web. Consider this. You probably check your email and credit card statements online without a second thought. However, this does not mean that accessing such sensitive information is without danger.
The surface web, often known as the open web
The “visible” surface layer is the open web, is known as the surface web. If we continue to imagine the web as an iceberg, the open web is the top piece that is above the sea. According to statistics, this collection of websites and data accounts for less than 5% of the whole internet.
This section contains all widely visited public-facing websites that can be browsed using standard browsers such as Google Chrome, Internet Explorer, and Firefox. Websites are often identified with registry operators like as “.com” and “.org” and may be found using common search engines. Because search engines can index the web via visible connections, surface web websites can be found.
The Deep Web

The deep web is located under the surface and accounts for about 90% of all webpages. This would be the undersea portion of an iceberg, considerably bigger than the surface web. In fact, this hidden network is so vast that determining how many pages or websites are active is difficult.
Continuing the analogy, large search engines may be compared to fishing boats that can only “grab” webpages near the surface. Everything else is out of reach, from scholarly papers to private databases and more unlawful stuff. This deep web also contains the black web.
While much news sites use the terms “deep web” and “black web” interchangeably, most of the deep web is completely legal and secure. The following are some of the most populous areas on the deep web:
- Databases: both public and private file collections that are not linked to other sections of the web and may only be searched within the database itself.
- Intranets are private networks used by businesses, governments, and educational institutions to communicate and regulate things within their organisations.
If you’re wondering how to go to the deep web, chances are you already do. All web sites that are unidentified by search engines are referred to as “deep web.” Deep web sites may be protected by passwords or other security barriers, while some simply instruct search engines not to “crawl” them. These pages are more hidden for a variety of reasons when there are no apparent connections.
The “hidden” information on the bigger deep web is often cleaner and safer. The deep web includes anything from draught blog entries and pending web page redesigns to the pages you reach when you bank online. These do not endanger your computer or your safety.
Others go a step farther, downloading unauthorised music or stealing movies that aren’t yet in cinemas. The most dangerous information and activities may be found on the dark side of the internet. Tor websites are at the extreme end of the deep web, which is referred to as the “black web” and can only be accessed with an anonymous browser.
Deep web safety is more important to the typical internet user than dark web safety because you might accidentally wind yourself in harmful areas: many parts of the deep web can still be accessed using standard internet browsers. This is how people might get up to a pirate site, a politically extreme forum, or watch frighteningly violent stuff if they follow enough tangential paths.
Also Read, Block Chain Technology? The future of Finances?
The Dark Web

The term “dark web” refers to websites that are not indexed and can only be accessed with specialist web browsers. The dark web, which is much smaller than the little surface web, is considered a subset of the deep web. Using our ocean and iceberg analogy, the dark web would represent the buried iceberg’s bottom tip. The dark web is an extremely hidden part of the deep web that few would ever interact with or even see. The deep web encompasses anything under the surface that can still be accessed with the proper tools, including the dark web.
Breaking down the dark web’s architecture exposes a few essential layers that contribute to its anonymity:
- There is no indexing of webpages by surface web search engines. Google and other mainstream search engines cannot locate or display results for pages on the dark web.
- A randomised network infrastructure is used to create “virtual traffic tunnels.”
- Because of its one-of-a-kind registry operator, it is inaccessible to ordinary browsers. It is also obscured by different network security mechanisms, like as firewalls and encryption.
The dark web’s reputation has frequently been associated with criminal intent or unlawful material, as well as “trading” sites where users may gain illicit items or services. However, legal parties have also made advantage of this structure.
Deep web hazards differ from dark web dangers for dark web safety. Illegal online activity is not always easy to find, but when you do, it is considerably more intense and dangerous. Before we get into the risks of the dark web, let’s look at how and why people visit these sites.
Is using the dark web illegal?

Simply, accessing the dark web is not unlawful. In reality, certain usage is totally legal and contributes to the “dark web’s” usefulness. Users on the dark web might seek three distinct advantages from its use:
- Anonymity of users
- Services and websites that are almost untraceable
- Capability to engage in criminal behaviour for both consumers and suppliers
As a result, the dark web has drawn many people who would otherwise be jeopardised if they revealed their names online. Victims of abuse and persecution, whistleblowers, and political dissidents have all used these covert sites. However, these advantages may readily be extended to individuals who choose to operate outside of the limits of the law in more overtly criminal ways.
When seen through this perspective, the legality of the dark web is determined by how you, as a user, interact with it. For a variety of reasons crucial to the preservation of liberty, you may find yourself on the wrong side of the law. Others may act illegally for the security and safety of others. Let’s go down each of these ideas in terms of the “dark web browser” and websites.
How to Access the Dark Web
Previously, the dark web was the domain of hackers, law enforcement officials, and cybercriminals. However, new technology like as encryption and the anonymization browser software Tor now allow anybody who wants to go dark to do so.
The Tor network browser (“The Onion Routing” project) allows users to view websites via the “Onion” registry operator. This browser is a service developed by the United States Naval Research Laboratory in the late 1990s.
Recognizing that the nature of the internet implied a loss of privacy, an early version of Tor was developed to conceal espionage communications. The framework was eventually repurposed and made public in the browser’s form we know today. It is available for free download to everyone.
Consider Tor to be a web browser, similar to Google Chrome or Firefox. Notably, rather of choosing the shortest way between your machine and the deepest areas of the web, the Tor browser takes a random routing of encrypted servers called as “nodes.” This enables users to access to the deep web without concern of having their activity recorded or their browser history revealed.
Deep web sites also utilise Tor (or related software such as I2P, the “Invisible Internet Project”) to stay anonymous, which means you won’t be able to find out who runs them or where they’re located.
Is it unlawful to use Tor?
Tor and other anonymous browsers are not exactly banned in terms of software. These ostensibly “black web” browsers are not limited to this area of the internet. Many people now use Tor to surf the public Internet and the deeper portions of the web in secret.
In today’s digital era, the anonymity provided by the Tor browser is critical. Corporations and governing organisations alike are currently engaged in illicit cyber spying. Some people just don’t want government authorities or even Internet Service Providers (ISPs) to know what they’re doing online, while others have no option. Users in countries with tight access and user rules are frequently denied access to even public sites unless they utilise Tor clients and virtual private networks (VPNs).
Regardless of the browser’s legality, you may still engage in criminal activities within Tor that might lead to your arrest. Tor may pilfer copyrighted information from the deep web, exchange illicit pornography, or act in cyber terrorism. Using a legal browser will not bring your conduct into compliance with the law.
Threats found on the dark web

If you’re thinking about utilising the dark web for basic privacy, you might wonder, “Is the dark web unsafe to use?” Unfortunately, it may be a very hazardous place to be. The following are some frequent risks you may encounter when browsing:
Malicious software
Malicious software, or malware, is alive and well on the dark web. It is frequently provided in some portals to provide threat actors with tools for cyberattacks. However, it remains across the dark web, infecting unwary people just like it does on the rest of the internet.
The dark web lacks many of the social contracts that website operators employ to secure users on the rest of the internet. As a result, users may be exposed to some forms of malware daily, such as.
- Keyloggers
- Malware on botnets
- Ransomware
- Malicious phishing software
If you choose to explore any sites on the dark web, you risk being identified out and targeted for hacking and other crimes. Most malware attacks are detectable by endpoint protection software. If your computer or network connection is compromised, the hazards of online surfing might extend into the unplugged world. Anonymity is powerful with Tor and the dark web foundation, but it is not impenetrable. If someone investigates deep enough, any internet action might leave breadcrumbs leading to your identity.
Scams
Some purported services, such as professional “hitmen,” may just be hoaxes meant to take advantage of unsuspecting consumers. According to reports, the dark web provides a variety of criminal activities, ranging from hired killings to prostitution and arms trafficking.
Some of them are well-known, well-established hazards that circulate in this corner of the internet. Others may take advantage of the dark web’s reputation to defraud people of enormous quantities of money. Some dark web users may attempt phishing schemes in order to steal your identity or personal information for extortion.